EMV is not entirely safe at the point of sale, either. "It's not clear whether delivering EMV in its current form is a significant enough improvement to justify the huge expense of adopting it in the United States," says Tyler Moore, a professor of computer science and engineering at Southern Methodist University who has written about the economics of cybersecurity. He says that since its initial development 20 years ago, EMV has proven to be far less ironclad than many had hoped.
It's also possible that other countries had more to gain from smart cards. Sullivan notes that European countries have largely offline payment networks, while the U.S. card system was designed to be online, giving card networks the ability to remotely review and authenticate any transaction as it is being conducted. Smart cards allow for authentication to take place between the card and the terminal itself, granting greater security for countries without online payment networks, and it's not clear whether the marginal advantages for an online network would be as great.
"I think that part of the reason we are among the last countries to move to chip and PIN is that the online system already has features that help to control fraud that other countries haven't had," says Sullivan. But even if chip cards are not the ideal solution, most agree that the current system is due for some sort of upgrade.
According to the Nilson Report, the United States accounted for 47 percent of global card fraud losses in 2012, even though it made up only about 24 percent of global card volume.
"Because so much of the world has shifted to chip and PIN, hackers see the U.S. cards as weaker links because they are much easier to copy," says Moore. "It has made the U.S. a target."
Why, then, have we been slow to upgrade our defenses?
The Blame Game
In a 2001 paper, Ross Anderson, a security engineering professor at the University of Cambridge who launched the economic study of cybersecurity, wrote that lapses in security can be expected when "the party who is in a position to protect a system is not the party who would suffer the results of security failure."
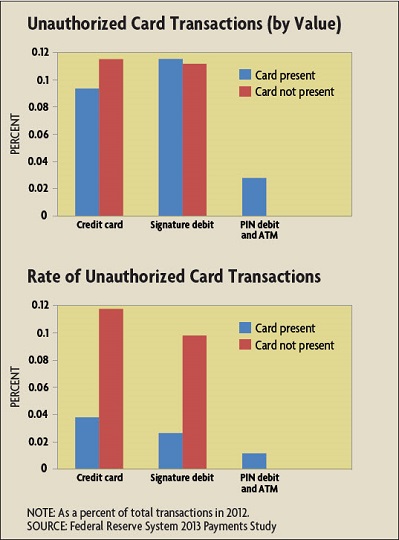
Who bears the costs of payment card fraud in the United States? Certainly consumers bear some. They must protect their personal information, replace compromised cards, and monitor suspicious activity on their accounts. But on the whole, American consumers are relatively well protected. Regulations E and Z limit consumer liability for fraudulent credit and debit transactions to $50, but in practice this is reduced to zero, as financial institutions generally make consumers whole. This could potentially lead to consumer negligence by reducing the incentive consumers have to be vigilant. But not everyone agrees the onus for fraud prevention should lie with consumers.
"It's very difficult for consumers to observe the security levels of the businesses they interact with," says Moore. "Because they cannot make decisions based on the security of the company, there's not a lot they can do to really protect themselves." As a result, it makes more sense for financial institutions and merchants, which have greater control over security, to bear liability. Moore's research supports this theory. In a paper documenting how liability for payment card fraud in the United Kingdom shifted to consumers after the introduction of EMV, he found that banks there spent much more on security and also suffered greater fraud than their American counterparts.
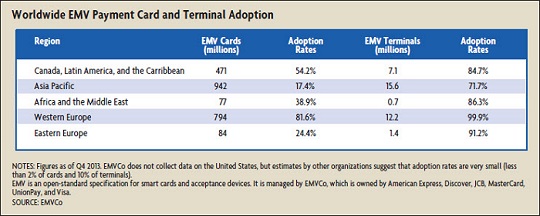
But banks and merchants disagree over who should bear the larger burden for fraud. According to the August 2013 Nilson Report, fraud costs in the United States are split between card-issuing financial institutions and merchants 63 percent to 37 percent. To the extent that card issuers control the network, it might seem appropriate that they shoulder most of the risk. But banks argue that costs are misaligned because the banking sector suffers far fewer breaches than retailers. According to data collected by the Open Security Foundation, businesses and retailers were subject to more than a quarter of security breaches worldwide in 2013, while financial organizations accounted for about 5 percent.
"There are clearly misaligned incentives," says Doug Johnson, vice president of risk management policy at the American Bankers Association. "When you have an organization on the retail side that is responsible for a lot more of the breaches but less than half of the costs of those breaches, they are going to have different incentives for security than financial service companies."
But retailers respond that, like consumers, they have little control over payment card security. Mallory Duncan, general counsel and senior vice president at the National Retail Federation, says security measures are determined by the card networks, and retailers are forced to accept vulnerable cards from the major networks because they have no alternatives.
"Most of the decisions are made within the financial services sector," says Duncan.
The disagreement over how to allocate cybersecurity responsibilities mirrors challenges economists have identified with public goods. Because security expenditures by one party can benefit others who didn't pay for them, the allocation of responsibilities to protect payments is complicated. In a 2005 paper, George Mason University professor of law Bruce Kobayashi wrote that while resources aimed at identifying and punishing cybercriminals might be more effective at improving society's overall security, such efforts are likely to be under-produced. This is because firms that invest in such security cannot exclusively capture all of the benefits; that is, there are "positive externalities" to such investments. Because of this, some firms might attempt to free ride on the security expenditures of others, reaping the benefits without paying any of the costs. Foreseeing this problem, individual firms are more likely to invest in security measures that protect themselves (such as antivirus software or firewalls) and deflect attacks to firms that have not made such investments.
At the same time, the costs from inadequate security do not fall wholly on the firm making investment decisions; that is, a lack of investment in security imposes "negative externalities" on other firms. In this sense, cybersecurity can be likened to pollution. If you operate a factory that emits pollutants into the air, the people who live downwind from you might be the ones who bear the cost of that pollution rather than you. Similarly, individuals or firms who choose not to invest in strong security and connect infected computers to the Internet pass the costs of those decisions onto other users. As a result, overall payments security against cyberattacks may be determined not by collective effort but by the weakest links.
Indeed, security blogger Brian Krebs, who first broke the news of the Target breach, reported in February that the malware used to infect Target's system was introduced through a third-party HVAC company. Large firms like Target may have the budget to fund extensive security, but they are still at risk due to smaller firms that either cannot afford adequate security or choose to free ride on the investments of others. To the extent that overall cybersecurity is determined by the weakest link, coordinated action may be crucial to improvement.
"It's kind of like getting the entire herd to move in one direction, and that can be difficult," says Mann.
Moving the Herd
The Target breach could provide the push for coordinated improvement of payments. Mann says that unlike in previous breaches, the reputational and stock market damage to Target has been large and persistent, perhaps placing greater pressure on retailers to upgrade their own systems or risk being next. The effect on the bank side has been significant as well, costing them about $200 million to reissue compromised cards.
"I think the needle has been moved," says Johnson. "I'm more hopeful now than I would have been a month ago because of the recognition by leadership on both the retail and financial services sides that we need to work together to solve a common problem."
In March, Visa and MasterCard announced a new cross-industry group to explore security improvements across networks. Setting standards could also help encourage collective action. The Payment Card Industry (PCI) Security Standards Council develops security guidelines for merchants, and in February, the National Institute of Standards and Technology released a framework for national cybersecurity standards in response to an executive order issued by President Obama last year.
But while financial regulators monitor and enforce risk standards on the bank side, no such enforcement exists for merchants. Standards developed by PCI are voluntary, and the organization has no authority to monitor or enforce compliance. Even when firms do comply, standards may fail to predict or adapt to ever-changing threats. In testimony, Target's chief financial officer said the company was compliant with PCI standards up until its breach.
Lack of enforced standards may not be entirely negative, though. "Sometimes creating a standard around which everyone can coalesce leads to greater efficiency,"says Mann. "But there's always a tension between standardizing around something that's known versus allowing multiple different solutions to flourish."
Indeed, standards meant to improve payments can slow adoption of new technology. The Durbin Amendment to the Dodd-Frank Act requires that merchants be given a choice between at least two PIN networks for transactions in order to improve competition. But because EMV was designed to work with only one PIN network, such a requirement has created a speed bump for chip and PIN in the United States. This may prove to be a blessing in disguise. Countries with fewer payment participants were able to quickly adopt EMV, but it's not clear that this has led to the long-run improvements they hoped for.
"We know from its deployment elsewhere that chip and PIN has quite a few limitations and demonstrated weaknesses," says Moore. "If we're going to spend billions of dollars on upgrading, we want to be developing a standard that's better than what's out there. For now, the United States has been the easiest target, but if everyone increases their security to a common level, EMV's known vulnerabilities will suddenly become economically viable."
Duncan notes that given enough competition in the payments space, the market can often find new security solutions. Merchants have begun exploring mobile payments using smartphones, banding together to design their own mobile payment network. (See "A Wallet in Every Phone," Region Focus, Fourth Quarter 2012.) Many banks already employ behavioral analytics to monitor customer transactions and alert them to any purchases that don't fit their spending profile. Some have also started exploring biometrics, such as fingerprint or voice authentication, to replace passwords and PINs. Ultimately, economists and industry insiders agree on one thing: Keeping ahead of the criminals requires collaboration.
"All the interested parties, representing consumers, merchants, card issuers, and networks, need to be talking to one another when making decisions," says Sullivan. "And they need to do it early."
Readings
"The 2013 Federal Reserve Payments Study - Recent and Long-Term Trends in the United States: 2000–2012." Federal Reserve System, December 19, 2013.
Data Loss Database, Open Security Foundation.
Gordon, Lawrence A., and Martin P. Loeb. Managing Cybersecurity Resources: A Cost-Benefit Analysis. New York: McGraw-Hill, 2005.
Kobayashi, Bruce H. "An Economic Analysis of the Private and Social Costs of the Provision of Cybersecurity and Other Public Security Goods." George Mason University Law and Economics Working Paper No. 05-11, 2005.
Mann, Catherine L. "Information Lost." National Bureau of Economic Research Working Paper No. 19526, October 2013. (Paper available online by subscription.)
Moore, Tyler, Richard Clayton, and Ross Anderson. "The Economics of Online Crime." Journal of Economic Perspectives, Summer 2009, vol. 23, no. 3, pp. 3-20.
Sullivan, Richard J. "The Changing Nature of U.S. Card Payment Fraud: Industry and Public Policy Options." Federal Reserve Bank of Kansas City Economic Review, Second Quarter 2010, pp. 101-133